Where does the future of 802.11 packet capture lie?
We are very familiar with performing 802.11 packet capture using USB wireless dongles as capture adaptors. The problem with USB adaptors is that they can only support up to 2 spatial streams due to limitations of the USB bus. With the advent of 3+ spatial streams APs, these USB dongles are no longer adequate capture adaptors. At the Wireless LAN Professionals Summit 2014, Jay Botelho, Director of Product Management, WildPackets, said that he sees capturing from access points as the future of 802.11 packet analysis. Capturing packets from an installed access point can provide an excellent approach for remote troubleshooting. But how about using an access point as a capture adapter connected directly to your laptop? Below I will show a procedure I used for capturing packets directly from an Aruba IAP-225 into WildPackets OmniPeek.
Setup
In the following example I have an Aruba IAP-225 running 6.3.1.0-4.0.0.0 connected directly to my laptop via an Ethernet cable. On my laptop I’m running OmniPeek version 7.9.1.

You will need to make sure you have configured an IP address on both the IAP-225 and your laptop. Test you have basic IP connectivity by pinging the access point from your laptop.
Procedure
Currently packet capture on Aruba Instant APs can only be configured from the cli. So you will need to SSH or Console to the access point.
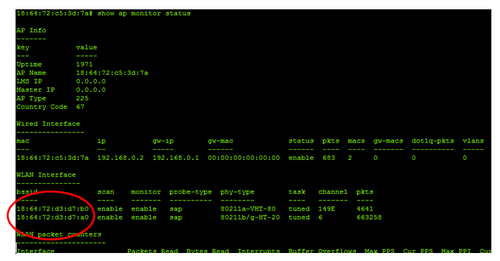
1) First we need to determine the BSSID of the radio we are would like to capture on. To do this we type the command: show ap monitor status . This command will display a whole wealth of information on the access point, but for this task we are only interested in the BSSID information shown in the figure below. We will see both the 2.4GHz and 5 GHz radio BSSIDs. Copy the BSSID for the radio you wish to capture from. For this example I’m going to use the 2.4GHz radio 18:64:72:d3:d7:a0
2) To start a packet capture on an Aruba IAP we use the following command:
pcap start <BSSID> <IP of capture tool> <port> <format> <max packet size>
In this example I’m going to capture from the 2.4Ghz radio 18:64:72:d3:d7:a0. The IP address of my laptop running OmniPeek is 192.168.0.10. I’m going to use port 5000, but you could use any port.
The format parameter is a number indicating the packet format. This allows you to send the packets in the correct format for the analyser of your choice. In this example I’m using WildPackets OmniPeek, but options for analysis such as Wireshark or AirMagnet exist. The different options for this parameter are shown below:
0 pcap, 1 peek, 2 airmagnet, 3 pcap radio, 4 ppi
Because I’m using OmniPeek I will choose 1 for peek format.
The last parameter is the maximum packet size, for this example I’m going to use a value of 2346. So for my example setup I would type:
pcap start 18:64:72:d3:d7:a0 192.168.0.10 5000 1 2346
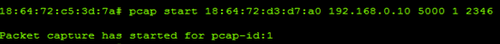
Notice the pcap-id is shown in the resulting message (see above). This id will be used when we issue the command to stop the capture. If you want the access point to capture both 2.4GHz and 5GHz traffic simultaneously then issue the pacp start command again but this time use the 5GHz radio BSSID.
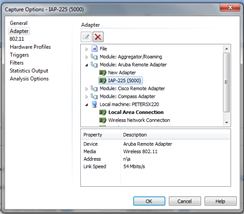
3) Next we need to start an Aruba Remote Adopter capture in OmniPeek. In OmniPeek select the ‘New Capture’ option from the Start Page. The Capture Options dialog will appear, on the Adapter tab choose ‘Aruba Remote Adapter’ and double click ‘New Adapter’
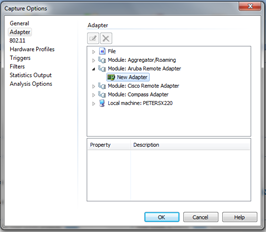
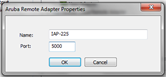
Enter a name and the port number. In this example I’m using port 5000. Click ok.
Make sure your newly created Aruba adapter is selected and click ok
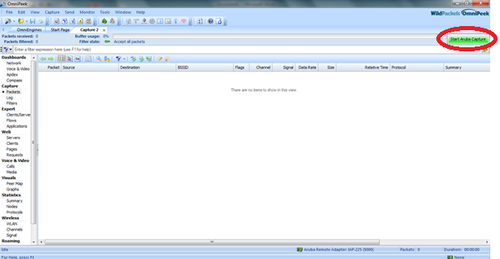
When the capture window opens click ‘Start Aruba Capture’
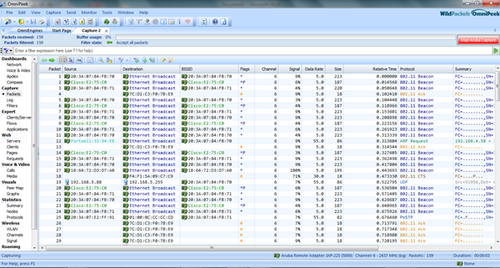
Your packets should now start to appear. Happy Analysis!
4) When you have finished capturing remember to stop the capture on the access point.
pcap stop 18:64:72:d3:d7:a0 1
In this command the digit 1 is the pcap id, this was displayed when I started the capture. If you can’t remember the pcap id then you can use the command show pcap to see your current captures.
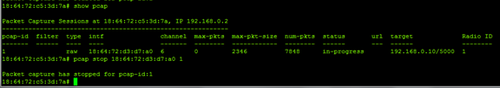
If you started a capture from the 5 GHz radio, then you will need to stop this one too.

